There’s a lot of stories in the media at the moment in light of revelations that certain government agencies can hack into your smartphone.
Whether it’s for spying on you for audio bits, capturing visual bits by turning your camera on without you ever knowing or just tracking your where abouts, it seems Smartphone hacking is hitting the mainstream.
Criminals have been looking for ways to exploit smartphones since they were invented way back when Steve Jobs released the first generation iPhone® on June 29th 2007.
Fast forward almost ten years and how our lives have changed because of that “light bulb” moment from Apple. Every year at the hackers convention Def Con held in Las Vegas these hackers are show casing how easy these technologies we use daily are open and vulnerable to hacking.
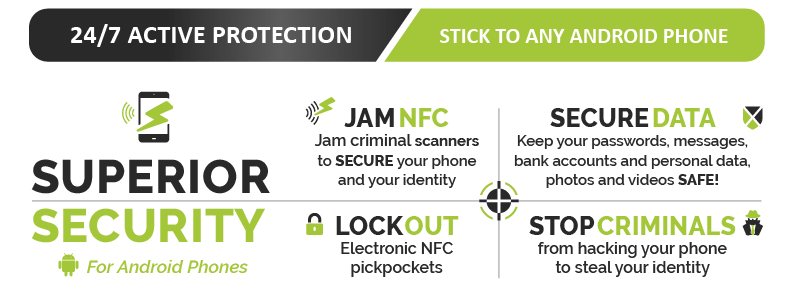
Find out how Armourcell™ can protect your Android phone
![]() The interesting thing is that most people who have ever used “Find My” feature for a lost phone, laptop etc is tapping into a form of surveillance. Whether it’s a partner tracking a spouse’s movements or downloading malicious code hidden in an app your kids just to downloaded to somebody walking past you in the street injecting malicious code via the backdoor through the NFC (Near Field Communication) or tap and go / bump feature located on most smartphones these days.
The interesting thing is that most people who have ever used “Find My” feature for a lost phone, laptop etc is tapping into a form of surveillance. Whether it’s a partner tracking a spouse’s movements or downloading malicious code hidden in an app your kids just to downloaded to somebody walking past you in the street injecting malicious code via the backdoor through the NFC (Near Field Communication) or tap and go / bump feature located on most smartphones these days.
The fact is with so much information on our smartphones its just way to tempting to not be exploited by criminals and let’s just say certain “agencies”.
As smartphone owners, we need to start stepping up security measures and that starts with simple things like two-stage pin security code, knowing what you’re downloading is from a reliable source, checking permissions of the apps your downloading etc.
 The harder thing to monitor is walk-by NFC injections, this is when somebody injects a malicious code into your phone via the NFC feature that tells your phone to do something (like next time your in a wifi zone, your phone is fooled to back up, then boots up a browser in the background to a malicious web address that copies all your files to the server) Scary stuff and everything & I mean everything is worth money on the dark web or deep web.
The harder thing to monitor is walk-by NFC injections, this is when somebody injects a malicious code into your phone via the NFC feature that tells your phone to do something (like next time your in a wifi zone, your phone is fooled to back up, then boots up a browser in the background to a malicious web address that copies all your files to the server) Scary stuff and everything & I mean everything is worth money on the dark web or deep web.
At Armourcard™ we knew this vulnerability was coming and that’s why we developed our latest product called Armourcell™ which utilises our patented micro jamming technology found in our original Armourcard product and applies it to your Android smartphone.
Armourcell™ effectively shuts the NFC backdoor into your phone and also stops your phone acting as a sniffer via the NFC feature for credit card data out in the open.